Greenhouse Software takes account security seriously, and restricts Greenhouse employees from accessing your organization's Greenhouse Recruiting account and associated information without your explicit consent. In some cases, the Greenhouse Technical Support team might require temporary access to your user account to complete troubleshooting, or to answer questions related to account-specific content.
Grant, revoke, or edit temporary account access
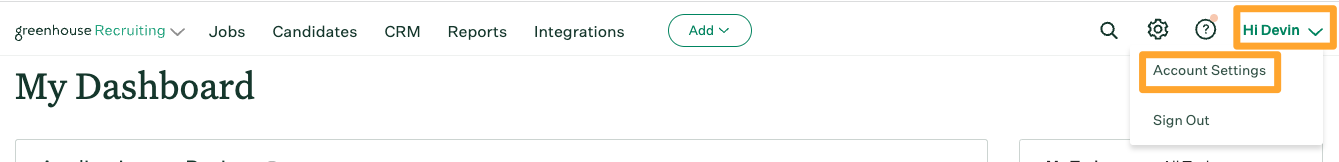
To grant temporary access to your account, click your initials on your navigation bar, then click Account Settings in the dropdown.
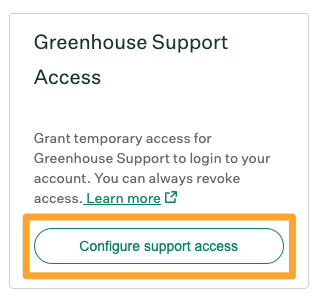
From the Account Settings page, navigate to the Greenhouse Technical Support Access panel on the right side of the page. Click Configure support access.
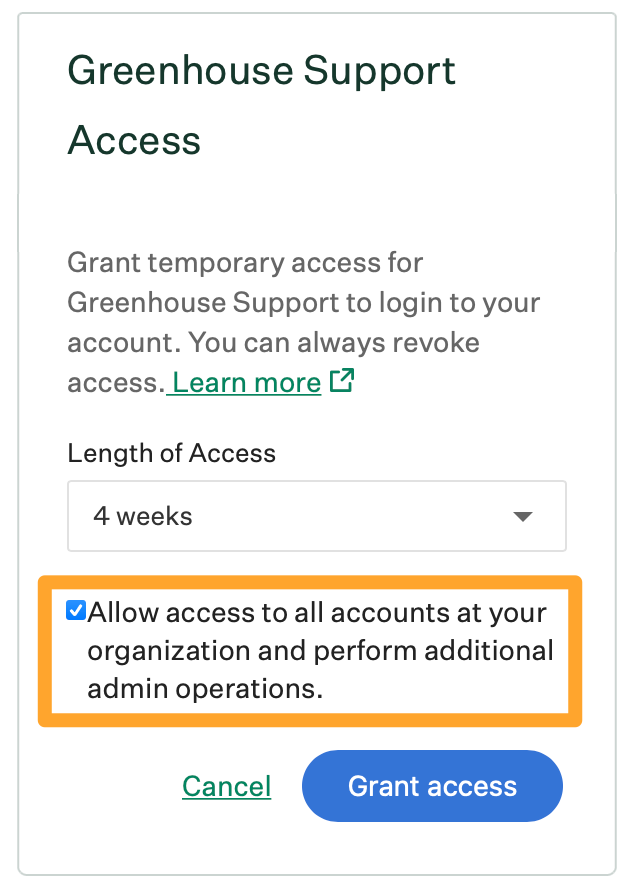
In the Length of access dropdown, select the duration of account access to grant the Greenhouse Technical Support team. Click Grant access when finished.
Note: Site Admin users have an additional option to Allow access to all accounts at your organization and perform additional admin operations.
Selecting this option permits Greenhouse Technical Support to log into your organization's account through any user account and to perform additional admin operations, such as enabling integrations your organization will utilize within your interview plan. Click here to learn more.
If you are a Site Admin, the Greenhouse Technical Support team might contact you by email if a non–Site Admin member of your team submits a request that requires org-wide access.
Temporary access is granted to the Greenhouse Technical Support team for the selected length of time. At the end of the selected time, access is revoked automatically from the Greenhouse Technical Support team.
Note: When you grant access, you are granting general access to the Greenhouse Technical Support team. This access is not limited to a specific Greenhouse employee.
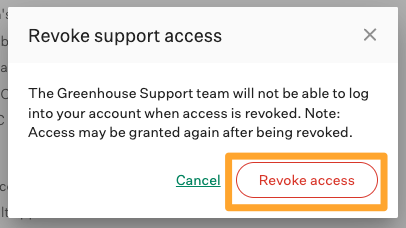
To revoke access before the selected end time, return to the Account Settings page > Temporary access panel and click Revoke access.
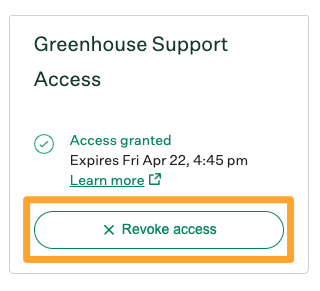
In the subsequent dialog box, click Revoke access to confirm. The Greenhouse Technical Support team can no longer access your account.
Note: To edit the length of access after granting it, follow the steps above to revoke access entirely, then grant new access with the updated duration.
Allow access to all accounts at your organization
When granting temporary access, Site Admins have an option to Allow access to all accounts at your organization and perform additional operations.
Selecting this option permits the Greenhouse Technical Support team to log into your organization's Greenhouse Recruiting instance through any user account, as well as edit your organization's BCCs, integrations, allowed filetypes, and session timeouts.
You are also granting access to data migration functionality including starting a new candidate or a new job migration, and the ability to email org data and email an all jobs summary report.
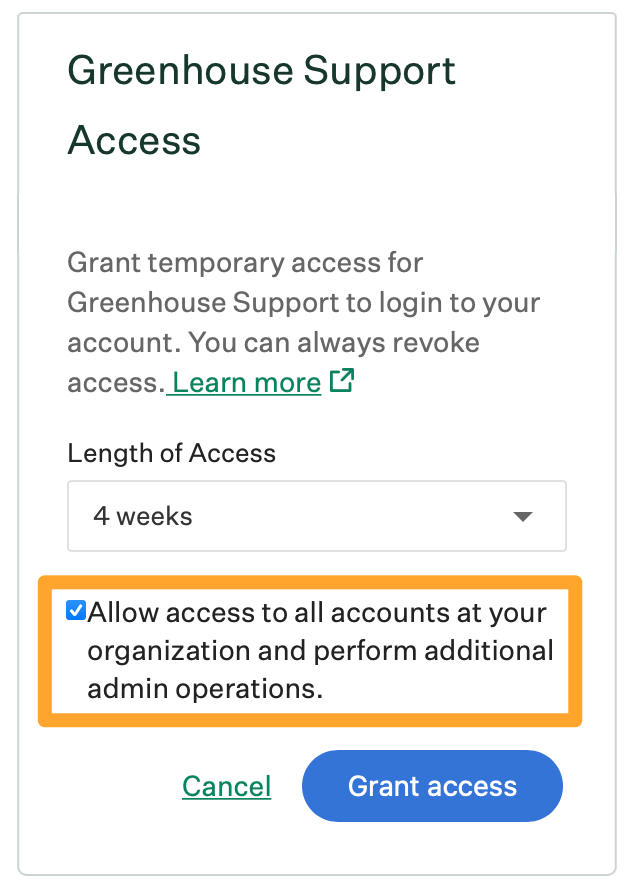
If this box is not checked, the Greenhouse Technical Support team can log into your organization's account through your user account only.
Any time a Site Admin grants universal access through all user accounts, all Site Admins at the organization will be notified via email.
Implications of granting temporary account access
Greenhouse employees access your account only as necessary. Granting temporary account access allows members of the following teams to log into your user account:
- Customer Success
- Technical Support
- Engineering
- Professional Services
If the permission Allow access to all accounts at your organization and perform additional operations is checked, you are granting edit access to your organization's BCCs, allowed filetypes, and session timeouts, as well as all data migration functionality including the ability to start a new candidate or a new job migration, and the ability to email org data and email an all jobs summary report.
Review record of Greenhouse employee logins
Your organization's Change Log creates a record any time a Greenhouse employee logs into a user's account. To review Greenhouse employee logins for your organization, have a Site Admin navigate to Configure ![]() > Change Log.
> Change Log.
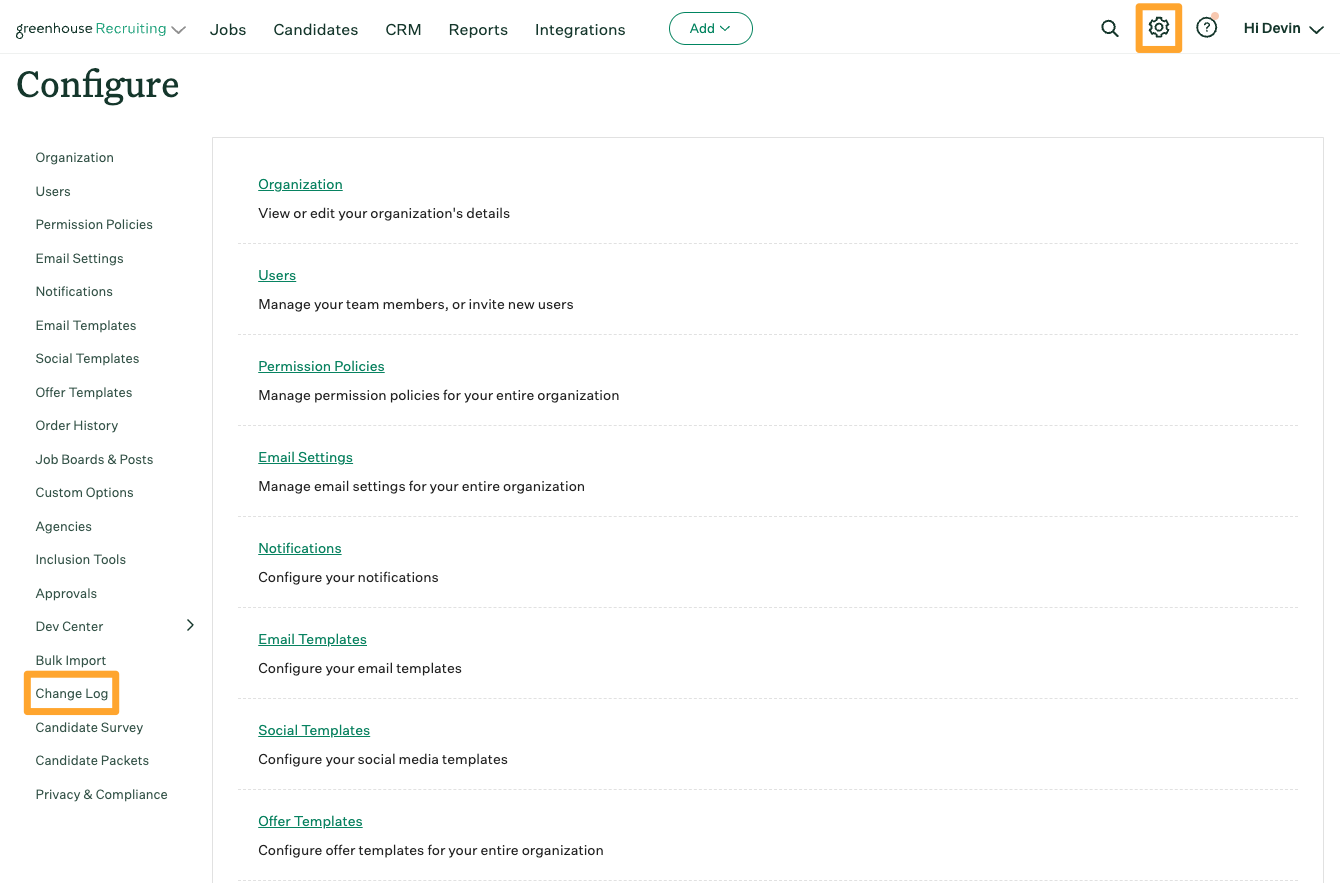
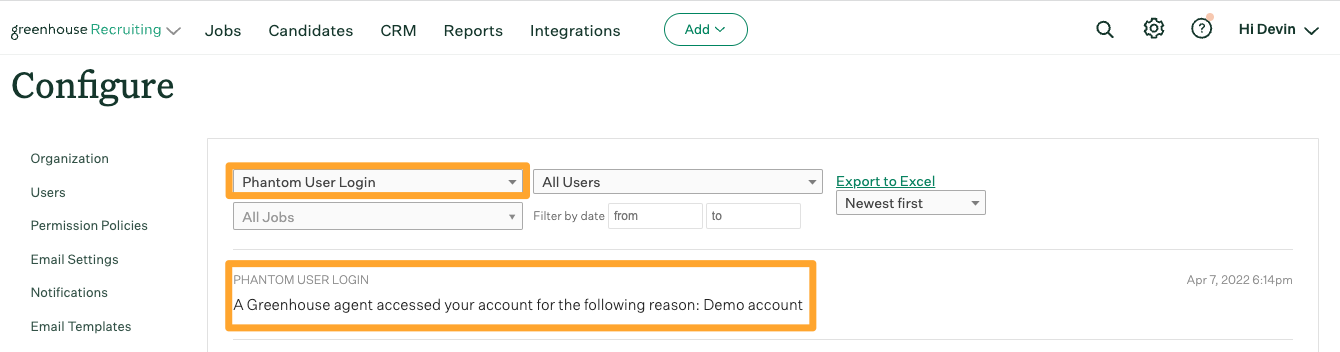
From the Change Log page, use the All Actions dropdown to search for Phantom User Login to see a list of all instances in which a Greenhouse employee has accessed your organization's Greenhouse Recruiting account.
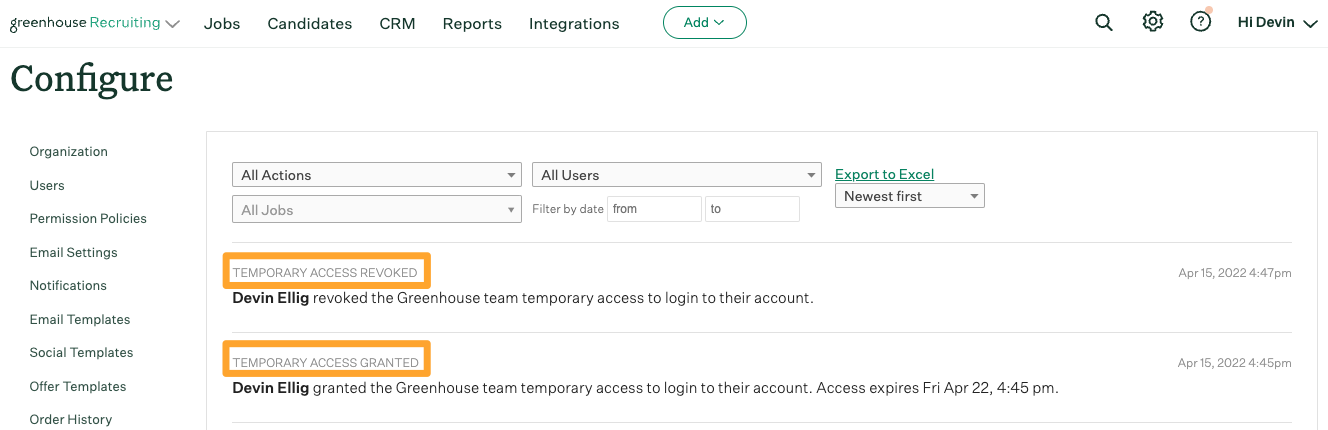
To audit for when temporary access was granted or revoked by a member of your team, search the All Actions dropdown for Temporary Access Granted or Temporary Access Revoked.
Click here to learn more about using the Change Log.
Cases where Greenhouse does not require consent for account access
In limited scenarios, Greenhouse Software can access your organization's account without a user first granting temporary access. This includes emergency situations and can be completed only by a select number of Greenhouse employees. This type of access is tracked closely by Greenhouse's Security team.
The Greenhouse Data Migrations team and Implementations team can access every newly created account for 90 days after the account is created without a user granting temporary access. After the first 90 days, members of these teams can no longer log into your account unless a user grants them temporary access.